What Really Happens When You Click Pay: The Invisible Mechanics of Digital Transactions
March 8, 2026
12 min

What Really Happens When You Click Pay: The Invisible Mechanics of Digital Transactions. You click a button. A tiny loading spinner appears. A second or two passes. A success message flashes. To the buyer, the experience feels seamless. Money simply moves from point A to point B. But beneath that simple interaction lies a complex choreography. Systems, networks, and algorithms communicate in milliseconds. Understanding this infrastructure is the key to solving hidden revenue leaks. For digital merchants, ignoring what happens inside that loading spinner often leads to unexplained checkout issues and lost customers. What feels like a simple click is actually a high-speed negotiation involving multiple global financial entities, all deciding whether to trust the transaction.
We tend to view the digital checkout as a utility, much like flipping a light switch. You turn it on, and the power flows. However, the reality of the payment processing flow is much closer to a high-speed relay race run over a constantly shifting obstacle course. Every participant in this relay has their own rules, their own risk tolerance, and their own legacy technology stack. When everything aligns perfectly, the race is won in under three seconds. When it does not, businesses are left dealing with frustrated customers, abandoned carts, and compounding revenue gaps.
To understand how to plug these leaks and operate a more resilient financial infrastructure, it is necessary to pull back the curtain on the exact sequence of events that triggers the moment a customer decides to buy.
1. The Millisecond Marathon
When a customer submits their payment details, the data embarks on a journey that spans multiple organizations and often multiple continents. While the entire process feels instantaneous to the person staring at the screen, it is actually a sequential exchange of structured data passing through several distinct gatekeepers.
The journey begins at the gateway. Think of the gateway as the translator and the initial security guard. Its primary job is to take the raw payment details inputted by the customer, encrypt them securely, and format them into a standardized message. The gateway does not move money; it simply packages the request and hands it off to the acquirer or acquiring bank.
The acquiring bank acts as the merchant’s financial representative in this ecosystem. It receives the encrypted payload from the gateway and routes it to the appropriate card network. The card networks act as the vast, global highways of the financial system. They govern the rules of the road, set the interchange rates, and ensure that a message from a merchant in London can be seamlessly understood by a bank in Tokyo.
Finally, the network delivers the request to the issuer. The issuing bank is the financial institution that gave the customer their credit or debit card. They are the ultimate decision-maker. The issuer holds the customer’s funds, and more importantly, they bear the primary liability if the transaction turns out to be fraudulent.
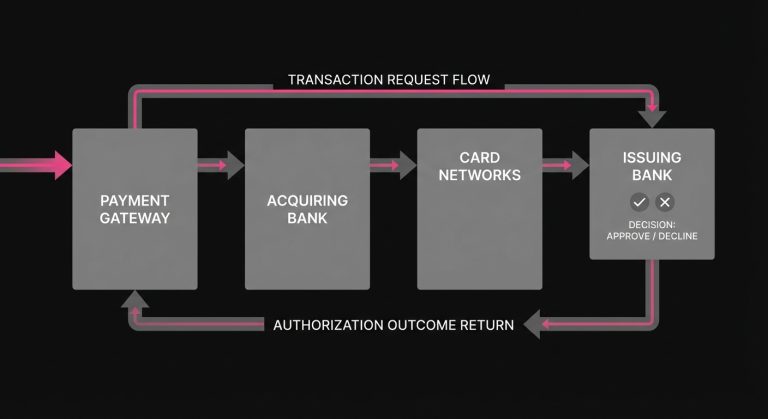
This entire relay-from the merchant’s website, to the gateway, to the acquirer, across the network, to the issuer, and back again-typically happens in the space of a deep breath. Yet, within those few milliseconds, the fate of the transaction is decided.
2. Inside the Mind of the Issuing Bank
To understand why transactions succeed or fail, you have to look at the process from the perspective of the issuing bank. This is where the actual payment authorization takes place, and it is an environment governed by probabilistic risk assessment rather than absolute certainty.
The issuing bank is playing a high-stakes game of incomplete information. When a transaction request arrives, they have mere milliseconds to answer three critical questions. First, is the account valid and active? Second, does the account hold sufficient funds or credit to cover the purchase? Third, and most difficult, is the person initiating this transaction actually the legitimate cardholder?
To answer that third question, issuers rely on complex, automated risk models. These models evaluate dozens of data points in real time. They look at the velocity of purchases, the geographic location of the request, the card network, and the historical spending behavior of the cardholder. If a customer who typically buys groceries in Chicago suddenly attempts to purchase high-end electronics from an IP address in Eastern Europe at three in the morning, the risk model will aggressively flag the anomaly.
However, issuers operate with a significant blind spot. They only see the data formatted in the standard payment message. They do not see the customer’s browsing history on the merchant’s site, their past login behavior, or their loyalty program status. Because they lack this contextual data, issuers must err on the side of caution. If a transaction looks moderately suspicious, or if the merchant falls into a statistically high-risk category, the issuer’s algorithms are designed to protect the account holder by declining the charge. In practice, payments fraud is widespread enough that 79% of U.S. businesses were hit by payments fraud in 2024 (Source).
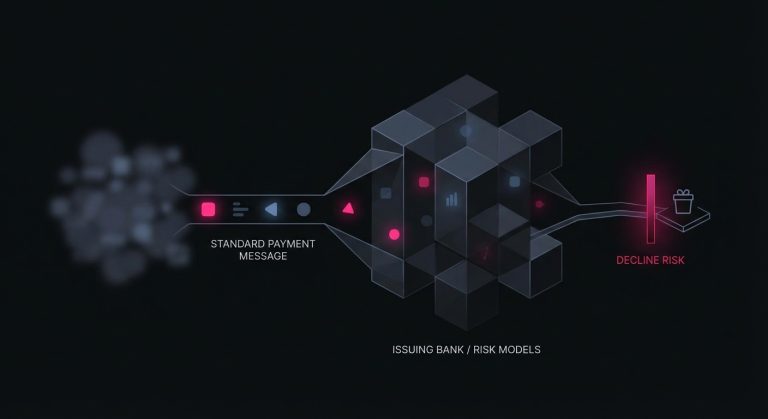
This cautious approach inevitably leads to false positives-legitimate transactions that are blocked because they vaguely resemble fraudulent patterns. For the issuing bank, a false positive is a minor customer service friction; for the merchant, it is a direct loss of revenue.
3. Translating the Anatomy of a Decline
When the issuing bank decides against approving the transaction, the message travels back down the chain, ultimately resulting in a transaction declined notification on the checkout screen. But the information provided to the merchant about why the failure occurred is often remarkably sparse.
The financial system communicates using standardized numerical codes known as an decline code. In an ideal world, these codes would provide clear, actionable feedback. In reality, they are often vague, generalized, or historically antiquated.
Hard Declines Versus Soft Declines
Experienced payment professionals generally categorize these responses into two distinct groups: hard declines and soft declines. Understanding the difference is foundational to any optimization strategy.
Hard declines represent a structural, permanent failure. This occurs when the card has been reported lost or stolen, the account has been closed, or the card number itself is invalid. In these scenarios, the door is firmly shut. Attempting to process the payment again will yield the exact same result. The only path forward is to ask the customer for a completely different payment method.
Soft declines, conversely, are temporal and contextual. These occur for reasons that may change if the transaction is attempted again later. The most common example is an insufficient funds response. A customer might lack the funds on a Tuesday, but their paycheck clears on a Thursday. Other soft declines occur due to momentary network timeouts, temporary freezes placed by the issuer’s fraud system, or formatting errors in the transaction payload.

The Ambiguity of Risk Codes
The most frustrating challenge for merchants is the overarching ambiguity of generic risk codes. A significant portion of failed transactions are returned with codes like “05 – Do Not Honor.” This code essentially functions as a polite refusal to elaborate. The issuer is stating that they will not process the charge, but they are deliberately withholding the specific reason, often to prevent malicious actors from reverse-engineering their fraud models.
When a card declined event features a generic code, the merchant is left guessing whether the issue is a lack of funds, a perceived fraud risk, or a temporary system anomaly. This opacity makes the process of recovering the transaction significantly more difficult.
4. The Ripple Effect of Frictional Failures
The impact of these rejections extends far beyond a single missed sale. A broken payment experience creates a ripple effect that damages marketing efficiency, customer loyalty, and long-term business health.
When a customer encounters payment issues at the final stage of checkout, all the resources spent acquiring that customer-the digital advertising, the brand building, the user experience design-are effectively wasted. The customer has demonstrated the highest possible intent to buy, only to be blocked by invisible infrastructural friction. While some buyers will patiently dig into their wallet for a second card, a significant percentage will simply abandon the purchase and move to a competitor with a smoother checkout flow.
The Nuance of Recurring Revenue
The problem becomes even more pronounced in recurring business models. For businesses that rely on renewals, subscription payment issues represent one of the largest hidden drains on growth.
In a subscription model, the customer is not actively present during the renewal process. The transaction happens in the background. If a payment failures event occurs during a monthly renewal, it is rarely because the customer explicitly decided to cancel. More often, it is an involuntary churn event. Their card may have expired, their bank may have updated their fraud parameters, or a temporary network timeout may have disrupted the authorization.
If the merchant fails to recover that transaction, they lose not just a single month’s revenue, but the entire remaining lifetime value of that customer. The user did not actively choose to leave the service; their payment method simply failed, and the merchant’s infrastructure lacked the sophistication to gracefully save the relationship.
5. The Danger of the Brute Force Approach
When faced with a high volume of soft declines, the natural instinct for many operations teams is to simply try the charge again. If the first attempt failed, perhaps the second or third will succeed. This leads to the implementation of basic, automated retry loops, where the system blindly attempts to process the card every twenty-four hours until it works or the customer is canceled.
While this brute force approach may occasionally catch a successful transaction, it is fundamentally flawed and actively harms the merchant’s broader payment health.
First, there are direct financial costs. Processors and networks charge fees for every authorization attempt, regardless of whether it is approved or declined. Blindly looping failed transactions rapidly inflates operational costs. Furthermore, card networks closely monitor the behavior of merchants. If a merchant repeatedly hammers a declined card, the network may impose punitive fines for excessive retries.
More critically, brute force retries damage the merchant’s reputation with issuing banks. Issuers monitor the ratio of approved to declined transactions coming from specific merchants. If a merchant exhibits a pattern of rapidly attempting to retry failed payments without any logical spacing or contextual changes, the issuer’s algorithms may begin to view the merchant itself as a risk vector.
This degradation of trust creates a vicious cycle. As the merchant’s reputation drops, the issuer’s risk models become stricter, leading to an even higher rate of declines across all of the merchant’s transactions, including those from healthy, well-funded customers. To truly reduce payment declines, a merchant must abandon brute force and adopt a more sophisticated, analytical approach.
6. The Logic of Intelligent Orchestration
The alternative to brute force is strategic payment optimization. This approach recognizes that every transaction is contextual, and the likelihood of a successful approval fluctuates based on a wide array of temporal and structural variables. Instead of asking “how quickly can we try again,” optimized systems ask “when is the optimal moment to request this specific authorization from this specific issuer?”
Intelligent recovery relies on interpreting the subtle signals hidden within the payment data. For instance, analyzing the historical success rates of specific issuing banks might reveal that a particular bank in Europe frequently times out during a specific maintenance window on Sunday nights. Attempting a retry during that window is futile.
Similarly, timing plays a massive role in recovering insufficient funds declines. An intelligent system does not retry a depleted debit card the very next day. Instead, it waits for predictable liquidity events, such as the first or fifteenth of the month, or specific days of the week that historically align with payroll deposits in the cardholder’s region.
This is where specialized technology becomes necessary. Platforms like SmartRetry act as a natural extension of a merchant’s payment stack, focused entirely on the science of payment optimization and intelligent retries of declined transactions. By leveraging data models to map issuer behaviors, map decline codes to specific recovery timelines, and dynamically adjust the pacing of attempts, these platforms help merchants seamlessly recover revenue and improve transaction approval rates without risking network penalties or damaging their issuer standing.
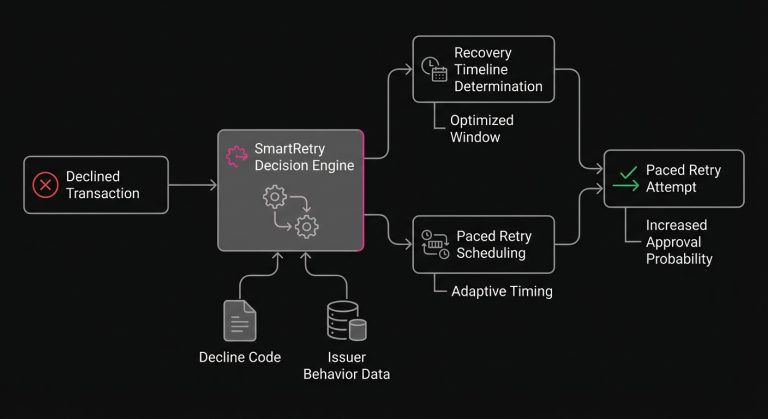
The Role of Data Formatting
Optimization also extends to the payload itself. Sometimes, the key to payment recovery is not changing when the transaction is sent, but how it is packaged. Ensuring that recurring indicators are correctly flagged, that network tokens are utilized instead of raw account numbers where applicable, and that the appropriate authentication data is included can drastically alter how the issuer’s risk model views the request.
By analyzing the specific characteristics of the initial failure-down to the Bank Identification Number (BIN) level-merchants can dynamically adjust the routing or the messaging of the second attempt, transforming a likely decline into a confident approval.
7. Moving from Passive to Proactive Operations
Historically, the ability to process a digital transaction was viewed simply as a cost of doing business-a utility layer managed by the finance or IT department. However, as digital commerce has matured, the perspective of high-performing teams has shifted. The checkout is no longer just the end of the customer journey; it is a highly sensitive conversion point where marginal gains translate directly into compounding revenue.
The invisible infrastructure that powers our digital economy is inherently complex, fragmented, and probabilistic. Issuing banks will continue to refine their risk models, networks will continue to update their standards, and the baseline friction of digital transactions will constantly evolve. Merchants who view a declined transaction as a permanent dead end will continue to suffer from unseen leaks in their growth models. The scale of the ecosystem keeps rising too, with digital wallets projected to reach 5 billion users worldwide in 2026 (Source).
Conversely, organizations that approach the payment flow as an optimizeable surface area are able to turn infrastructural friction into a strategic advantage. By understanding the mechanics of authorization, respecting the risk constraints of the issuing banks, and applying intelligent, data-driven strategies to transaction recovery, businesses can protect the revenue they have already earned. Ultimately, the difference between a lost customer and a retained subscriber often comes down to understanding the quiet, millisecond negotiations that happen the moment they click pay.
Still letting failed transactions slip through?
SmartRetry turns declines into approvals - automatically, intelligently, and without changing your payment provider.
Frequently asked questions about this topic
Share this article
Author
Roi Lagziel
Roi Lagziel is a payments engineer specializing in authorization optimization, retry strategies, and issuer-level behavior. His work focuses on building practical, data-driven systems that help payment teams reduce false declines and recover lost revenue.
Read all articles >More in Payment Failures & Decline Codes:

March 8, 2026
The Hidden Mechanics of Cross-Border Card Declines
This article explains why international card transactions underperform, from issuer risk models to data mismatches and recurring billing gaps, and shows operators where to act to recover revenue and reduce false declines.

March 8, 2026
Issuer Response Code 43: Why Merchants Must Stop Retries on Stolen Cards
This article explains why Code 43 is a terminal decline, how to remove dead credentials from retry logic, and how disciplined handling protects approval rates, margin, and customer recovery.

March 8, 2026
Authorization Code 41: How Payment Teams Should Handle Lost Card Declines
This article explains why Code 41 is a definitive lost-card decline, how to stop harmful retries, and where account updater, tokenization, and targeted dunning improve recovery and authorization performance.