Issuer Response Code 43: Why Merchants Must Stop Retries on Stolen Cards
March 8, 2026
12 min

The Hard Stop: Why Issuer Response Code 43 Demands Complete Surrender
When a decline occurs, your first instinct is often to push back. Systems hiccup, networks time out, and funds can briefly dip below a threshold. In these cases, a carefully timed second attempt often saves the sale. However, the payment ecosystem is profoundly complex, and not all rejections are temporary roadblocks. Some decline codes are concrete walls. When a transaction returns a stolen card code, the rules of engagement change entirely. It is no longer a suggestion to wait. It is a mandate to stop.
Every payment professional eventually learns that persistence is only a virtue when applied to the right problems. Treating every payment failure as a temporary glitch reveals a fundamental misunderstanding of how card networks operate. When an issuing bank transmits a specific terminal decline code, they are sending a definitive signal that the payment credential is dead. Continuing to knock on a door after the locks have been changed does not just waste time. It actively damages your standing within the broader financial network.
Understanding how to interpret, handle, and gracefully recover from these terminal signals is what separates sophisticated payment operations from blunt-force billing engines. To master this aspect of revenue recovery, we have to look closely at what happens behind the scenes when a card is flagged as compromised.
The Anatomy of a Terminal Response
When a customer initiates a purchase, a complex conversation happens in milliseconds. The merchant asks the acquirer to facilitate the charge. The acquirer then formats the request and sends it across the card network to the issuing bank. From there, the issuer evaluates the request against a massive set of variables like available balance, purchase velocity, geographic location, and the fundamental status of the account.
During this authorization process, the issuer ultimately returns a two-digit code. Most merchants are familiar with common soft declines like insufficient funds or generic processor errors. These are circumstantial rejections where the card itself is valid, but current conditions prevent the transaction from proceeding.
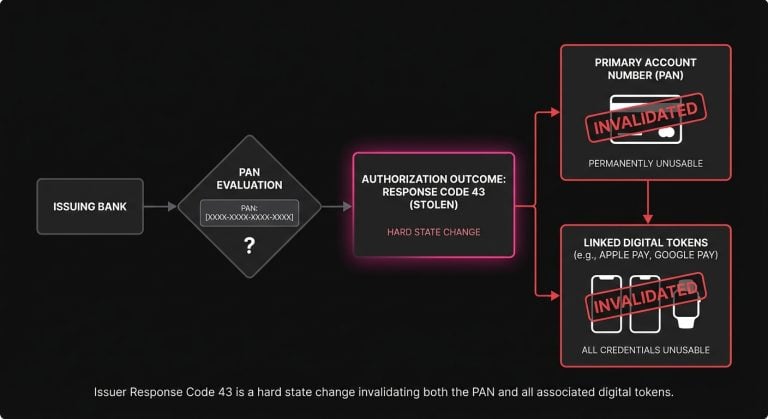
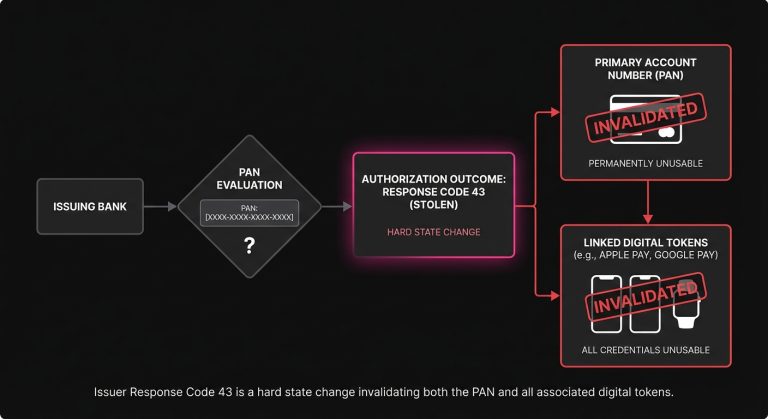
Issuer Response Code 43 is different. This code specifically translates to a stolen card, meaning the primary account number or PAN has been actively flagged in the issuer’s core system as compromised. This usually happens because the cardholder called their bank to report a missing physical wallet, or because the bank’s internal fraud models detected unauthorized activity and proactively killed the credential.
Once this flag is set, the card is permanently deactivated. The physical card in the customer’s pocket is now useless, and any digital tokens tied directly to that specific PAN without automated updater logic are equally dead.
The False Hope of the Blind Retry
The natural instinct of many legacy billing systems is to retry failed payments on a predetermined schedule. If a charge fails on Monday, the system might try again on Wednesday and perhaps one last time on Friday. For a soft decline, this logic makes a certain amount of probabilistic sense because people get paid, balances clear, and temporary holds drop off.
Applying this same logic to a stolen card response is an operational disaster.
Unlike a transient error, a Code 43 will never magically resolve itself. The issuing bank is not going to reactivate a stolen card. When a merchant’s billing engine repeatedly pings the network with a credential that the issuer has explicitly stated is compromised, it sends a very specific message to the ecosystem. It tells them that this merchant does not listen to network signals.
This behavior introduces significant drag on your payment processing flow. Beyond wasting bandwidth, it actively degrades the health of your merchant identification number, or MID. Issuing banks run sophisticated machine learning models to determine which merchants to trust. If your MID is historically associated with ignoring terminal declines and constantly submitting dead tokens, the issuer’s trust in your traffic drops. As a result, when you send a perfectly valid transaction from a healthy card, the issuer’s risk model might view your request with heightened suspicion and subtly lower your overall approval rate.

The Financial Weight of Network Penalties
The consequences of poor retry logic extend beyond trust. Card networks like Visa and Mastercard strictly monitor how merchants handle terminal declines by categorizing decline codes and enforcing specific rules for subsequent authorization attempts.
Response Code 43 is universally classified as a hard decline. Network rules explicitly state that merchants must not attempt another authorization on a card that has returned this code, and violating this rule can trigger immediate compliance fines. Furthermore, every time a transaction is declined, the merchant generally still pays a small authorization fee to their processor. Running a doomed transaction several times through an automated billing loop essentially sets fire to your own margin while inviting network penalties.
Categorizing the Chaos: Hard Declines vs. Soft Declines
To build resilient operations, teams must map out exactly how their systems react to different categories of failure. A declined payment is simply raw data. It is up to the merchant to parse that data and route it through the appropriate logical flow.
Soft declines are transient, acting as invitations to try again later using optimized timing based on the customer’s historical payment patterns or known banking schedules. In contrast, hard declines are permanent state changes that require the immediate suspension of the billing cycle for that specific payment method.
Within the family of hard declines, Code 43 has a few close siblings that operate similarly but carry distinct nuances:
- Authorization Code 41 Similar to a stolen card, the cardholder has reported the card misplaced. The result is a permanent block, but the underlying assumption of immediate fraud risk is slightly lower.
- Code 04 (Pick Up Card): This is an aggressive signal where the issuer is essentially instructing the merchant to physically confiscate the card if it is presented in person. In the digital realm, it means the account is highly compromised or severely delinquent.
Regardless of the subtle differences in meaning, the operational response to codes 41, 43, and 04 should be identical. Merchants must stop billing immediately, strip the token from the active retry queue, and shift the burden of resolution back to the customer.
The Role of Intelligent Restraint
True payment optimization is not simply a matter of trying harder. It is a matter of trying smarter. A highly tuned revenue recovery strategy requires surgical precision, meaning you must aggressively pursue the transactions that can be saved while instantly abandoning the ones that cannot.
This is where specialized technology becomes necessary. Platforms like SmartRetry focus on payment optimization and intelligent retries, operating on the core principle that avoiding bad retries is just as critical as executing good ones. By automatically parsing issuer responses and instantly halting activity on terminal declines, these systems help merchants recover revenue where possible while protecting their overall approval rates from unnecessary damage. Intelligent logic ensures that your processing volume remains clean, efficient, and aligned with network mandates.
When your infrastructure is smart enough to act as a circuit breaker for dead tokens, your engineering and finance teams are freed from dealing with the cascading failures of blind retry loops.
Navigating the Account Updater Nuance
A common point of confusion among product managers and operational teams involves how terminal declines interact with automated card updater services. Both Visa Account Updater and Mastercard Automatic Billing Updater are designed to seamlessly provide merchants with new card details when an old card expires or is replaced.
If a customer’s card is stolen, their bank will issue them a new one with a new PAN. Therefore, merchants often assume they can just wait for the updater service to hand them the new credentials and resume billing.
While this is conceptually true, the timing and execution require careful handling.
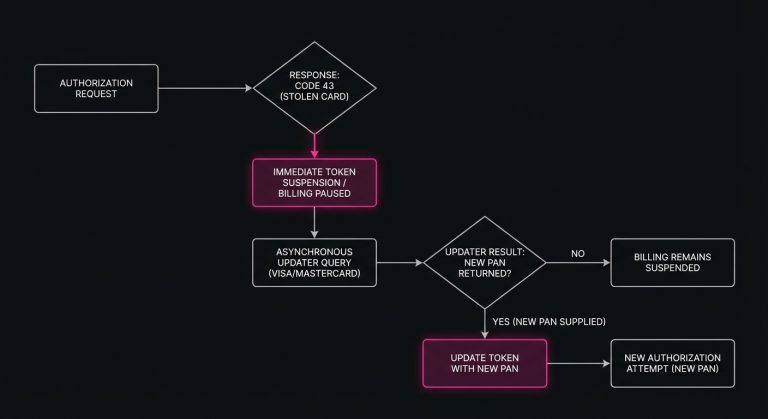
When a Code 43 is triggered, the old token is dead immediately. The new token might not be available in the updater database for several days. If your system continues to attempt authorizations on the compromised token while waiting for the updater service to kick in, you are still violating network rules and incurring penalties.
The correct logical flow is to suspend the token the exact moment the 43 response is received. The system should then query the account updater service asynchronously. Only when a distinctly new payment credential is provided by the network should a new authorization be attempted. If the updater service returns a negative response or fails to provide a new PAN within a reasonable window, the automated recovery path is officially closed.
Handling Subscription Payment Issues Gracefully
When a stolen card response occurs within a recurring revenue model, the challenge shifts from technical routing to customer experience management. Subscription payment issues are inherently delicate. The customer intended to pay you, but their primary financial instrument has been compromised, creating a situation that is already stressful for them.
The worst thing a merchant can do is silently suspend the account and wait for the customer to notice. The second worst thing is sending an aggressive, poorly worded automated email bluntly stating that their card was stolen.
If a customer simply froze a virtual card because they misplaced their physical wallet, seeing an email from a software provider claiming their card was stolen might cause unnecessary panic. Instead, the communication strategy must be tactful, clear, and action-oriented.
Crafting the Recovery Message
When your system logs a hard decline, it should immediately trigger a specific dunning sequence. The messaging should focus on the payment issues at hand without making definitive claims about the customer’s personal security.
Phrasing like “Your bank has indicated a problem with your current payment method” or “We were unable to authorize your card for this month’s cycle, please provide a new payment method to keep your account active” strikes the right balance. It informs the customer that action is required without causing unnecessary alarm.
Furthermore, the friction to update that payment method must be virtually zero. The email should contain a secure, authenticated link that drops the user directly into a specialized checkout flow designed specifically to capture the new card. If they have to log in, navigate to an account settings page, find the billing tab, and manually delete the old card before entering the new one, your chances of recovering that subscription drop precipitously.
Engineering a Smarter Checkout Experience
While most stolen card responses happen in the background during automated recurring billing, they occasionally surface during live active sessions. A customer might be attempting to purchase a new item using a saved card on file that they forgot they reported stolen a week ago.
Handling checkout issues in real-time requires a delicate touch. If the issuer response is a 43, your front-end application must instantly translate that into a user-friendly prompt rather than displaying raw error codes. A message reading “Error 43: Stolen Card” is jarring and unprofessional.
Instead, the UI should smoothly intervene with a message like, “This payment method cannot be used at this time. Please select or enter a different card to complete your purchase.”
By immediately rendering the compromised card unselectable in their digital wallet, you prevent the user from instinctively clicking submit and generating multiple hard declines in rapid succession. This seamlessly guides them toward a successful resolution while protecting your own processing metrics.
Reframing Payment Failures as Data Points
It helps to shift how an organization views a declined transaction. Rather than seeing it purely as a loss of immediate revenue, view it as a critical piece of database hygiene.
Over time, any mature merchant’s database fills up with outdated, expired, or compromised payment credentials. This digital rot slows down processing times, inflates billing queues, and skews financial forecasting. When an issuer hands you a definitive hard decline, they are actually doing you a favor by providing absolute certainty that a specific piece of data is no longer valid.
Instead of fighting this reality, use it to reduce payment declines across the board by purging the dead token, updating the customer record, and cleansing the database. When you maintain a pristine vault of payment tokens where every saved card is actively viable, your success metrics naturally improve. Your engineering resources are then spent building better products rather than managing the fallout of bloated retry queues.
The Broader Context of Merchant-Issuer Trust
The global payment ecosystem functions on a foundation of calibrated trust. Issuers must trust that merchants are submitting valid requests, while merchants must trust that issuers are making accurate authorization decisions. Acquirers and networks sit in the middle to enforce the rules that keep the system stable.
Every time you submit an authorization request, you participate in this ecosystem, and how you behave when a transaction is rejected is heavily scrutinized. Ignoring a stolen card response acts as a trust violation. It signals that your infrastructure is either too archaic to parse the response or your operations are simply too reckless to care.
Conversely, respecting network signals builds structural credibility. When your systems instantly back down from a hard decline, you align yourself with the issuer’s risk models and demonstrate that you are a sophisticated actor in the financial network. This alignment is rarely visible on a day-to-day basis, but it compounds over time, directly influencing how favorably your traffic is treated during peak volumes and edge-case scenarios.
Payment strategy is an ongoing exercise in balance. The tools available to merchants today are incredibly powerful, capable of saving vast amounts of revenue that would otherwise slip through the cracks of network latency or temporary funding shortfalls. However, that power must be governed by strict, unyielding logic. Recognizing when to push forward is a vital skill for any revenue team, but recognizing when a credential is truly dead and having the discipline to walk away gracefully is the hallmark of true operational maturity.
Still letting failed transactions slip through?
SmartRetry turns declines into approvals - automatically, intelligently, and without changing your payment provider.
Frequently asked questions about this topic
Share this article
Author
Roi Lagziel
Roi Lagziel is a payments engineer specializing in authorization optimization, retry strategies, and issuer-level behavior. His work focuses on building practical, data-driven systems that help payment teams reduce false declines and recover lost revenue.
Read all articles >More in Payment Failures & Decline Codes:

March 8, 2026
The Hidden Mechanics of Cross-Border Card Declines
This article explains why international card transactions underperform, from issuer risk models to data mismatches and recurring billing gaps, and shows operators where to act to recover revenue and reduce false declines.

March 8, 2026
Authorization Code 41: How Payment Teams Should Handle Lost Card Declines
This article explains why Code 41 is a definitive lost-card decline, how to stop harmful retries, and where account updater, tokenization, and targeted dunning improve recovery and authorization performance.

March 8, 2026
Decoding Authorization Code 59: How Suspected Fraud Declines Affect Payment Recovery
This article explains why issuers return Authorization Code 59, how false positives hurt conversion, and what payment teams can do to recover legitimate revenue without damaging approval rates.