Decoding Authorization Code 59: How Suspected Fraud Declines Affect Payment Recovery
March 8, 2026
12 min

Decoding Authorization Code 59: The Mechanics of Suspected Fraud
You have built a seamless digital experience where the customer navigates smoothly to your checkout, entering their payment details with anticipation. They click the final button to complete the purchase, but then the entire momentum stops. The screen hesitates, the data payload travels to the issuing bank, and the response comes back negative. You have a transaction declined message on your hands. While any rejection introduces friction into the payment processing flow, a specific subset of these failures requires a much more nuanced approach than a simple nudge to try again. When the system returns Authorization Code 59, you are no longer just dealing with insufficient funds or a typo in a billing address. Instead, you are dealing with suspected fraud.
Understanding how to navigate this specific response separates mature payment operations from those that simply guess their way through authorization failures. In the complex and highly probabilistic world of digital payments, an issuer throwing a fraud flag is a significant event. It indicates that a sophisticated, heavily guarded risk model has reviewed the transaction data and determined that the person clicking the buy button might not actually be the legitimate cardholder.
To effectively manage and optimize around this decline code, it is essential to step into the shoes of the issuing bank, understand the data signals that trigger these alarms, and construct a recovery strategy that respects the ecosystem’s rules while rescuing legitimate revenue.
The Invisible Math Behind the Issuer’s Decision
When a customer attempts a purchase, an incredible amount of data is packaged and sent through the payment gateway, the acquiring bank, and the card network before eventually landing at the issuer’s front door. The issuer has mere milliseconds to make a decision. There is no human reviewing the purchase. Instead, the entire process relies on highly trained, deeply complex machine learning models and heuristics.
These models evaluate hundreds of discrete data points in real time, analyzing everything from the cardholder’s historical spending patterns to the Bank Identification Number, time of day, device footprint, and the geographical location of the IP address compared to the billing address. They also review network-level data to assess broader trends across millions of other cards.
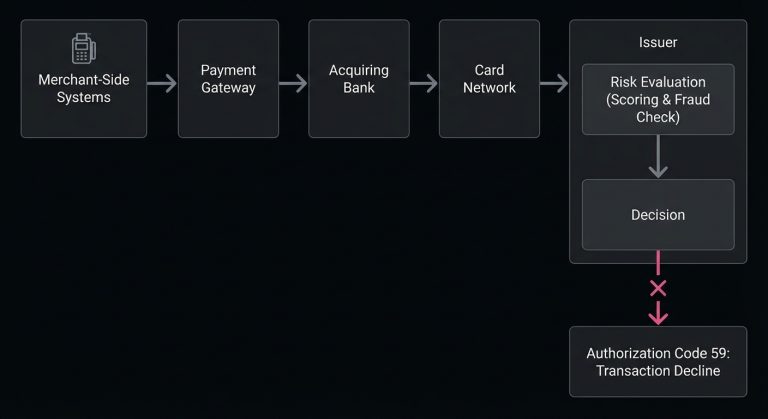
Authorization Code 59 is the output when this mathematical evaluation returns a risk score that exceeds the issuer’s acceptable threshold. The bank is essentially stating that while the card is valid and there are likely sufficient funds available, the context of the transaction looks too suspicious to approve. The bank is prioritizing the protection of its cardholder, along with its own liability, over the completion of the sale.
Unpacking the Common Triggers of Code 59
Issuers do not share the exact weighting of their risk algorithms, as doing so would allow bad actors to reverse-engineer their defenses. However, experienced payment professionals recognize common patterns and anomalies that frequently lead to a suspected fraud decline.
Velocity is one of the most common culprits. If a card is used for multiple rapid-fire purchases within a short window, especially across different merchants or for highly liquid digital goods, the risk score skyrockets. The bank’s model interprets this as a fraudster testing a stolen card or attempting to extract maximum value before the cardholder notices the unauthorized activity.
Geographical mismatches also play a heavy role. If a cardholder whose primary residence is in London suddenly attempts a high-value purchase from an IP address originating in a different country, the model flags the deviation. While travel is a normal part of life, sudden and uncharacteristic geographical leaps without prior travel notifications often trigger Code 59.
Data inconsistencies within the transaction payload itself frequently tip the scales. A mismatch in the Address Verification System or an incorrect Card Verification Value does not always result in an immediate hard decline for those specific reasons. Sometimes, when combined with other mild risk factors like a new device or an unusually large basket size, these minor mismatches compound. This pushes the overall risk score past the tipping point into suspected fraud territory.
The Heavy Cost of the False Positive
If every Code 59 accurately identified a criminal, managing it would be straightforward. The merchant could simply block the user, flag the account, and move on. The reality is far more complicated. Risk engines are inherently probabilistic, meaning they operate on likelihoods rather than absolute certainties.
Because banks often bear the financial liability for fraudulent credit card transactions, their models are typically tuned to be conservative. This conservative tuning inevitably catches legitimate customers in the net. A cardholder buying a high-end laptop while on vacation, a parent making a series of rapid purchases for back-to-school shopping, or a user who recently moved but hasn’t updated their billing address can all easily trigger a fraud decline.
These false positives represent one of the most expensive hidden leaks in e-commerce. When a legitimate customer faces payment failures due to overzealous fraud filters, the damage extends beyond the immediate loss of revenue. The customer often feels frustrated, embarrassed, or confused, which can lead them to abandon the cart entirely and switch to a competitor. They form a negative association with the merchant’s brand, entirely unaware that their own bank actually blocked the sale.
The Danger of the Unthinking Retry Loop
When faced with a decline, the instinct of many rudimentary payment systems is to immediately push the transaction through again. In some scenarios like network timeouts or momentary gateway glitches, a rapid retry makes sense. However, in the context of Authorization Code 59, it is one of the most damaging actions a merchant can take.
Think of an immediate retry on a fraud decline like aggressively pressing the button for an elevator that has already broken down. It does not make the elevator arrive faster, and it annoys the building management. When an issuer rejects a transaction for suspected fraud, submitting the exact same data payload seconds later does not change the risk assessment. In fact, it often makes the transaction look significantly more suspicious. Botnets and automated card-testing scripts are known for rapidly retrying failed transactions, and behaving like a botnet is a quick way to degrade your merchant trust score with issuing banks.
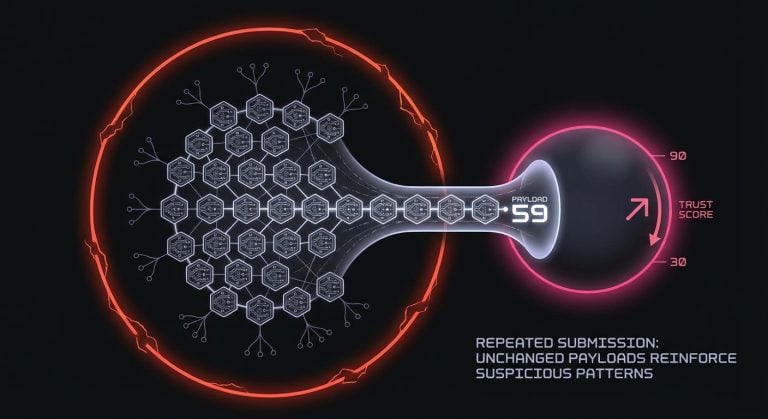
Repeatedly hammering an issuer with retried fraud declines can lead to broader authorization penalties. This can lead the issuer to view the merchant’s overall traffic as inherently risky, causing a depressed approval rate across the board even for perfectly legitimate, low-risk customers.
Architecting a Thoughtful Payment Recovery Strategy
Handling Code 59 requires stepping back from the immediate transaction and looking at the broader recovery workflow. The goal is to clear the issuer’s suspicion, which usually requires the introduction of new information or a deliberate pause in the process.
A strategic approach begins with timing. If an issuer suspects fraud, they frequently trigger an automated workflow on their end, such as sending a text message or an email asking the cardholder to confirm the attempt. This out-of-band authentication takes time because the cardholder needs a moment to look at their phone, reply to the security prompt, and wait for the bank’s system to clear the card’s status.
Attempting to recover this payment requires giving the customer the necessary breathing room to interact with their bank. A well-designed recovery flow might involve pausing the checkout process, guiding the user on what to do next, and implementing a calculated delay before any subsequent authorization attempt is made.
When managing these complex issuer responses, thoughtful infrastructure matters. SmartRetry operates as a platform focused on payment optimization and intelligent retries of declined payment transactions, helping merchants recover revenue and improve transaction approval rates. By analyzing the specific decline code and the context of the transaction, it applies the appropriate timing and logic for a retry rather than guessing in the dark. This systematic approach allows businesses to salvage legitimate sales while remaining respectful of the guardrails set by the issuing banks.
Shifting the Paradigm with Strong Authentication
One of the most effective ways to counteract an issuer’s fraud suspicion is to mathematically prove that the person at the keyboard is the actual cardholder. This is where Strong Customer Authentication and other forms of strong customer authentication become incredibly valuable tools in the payment optimization toolkit.
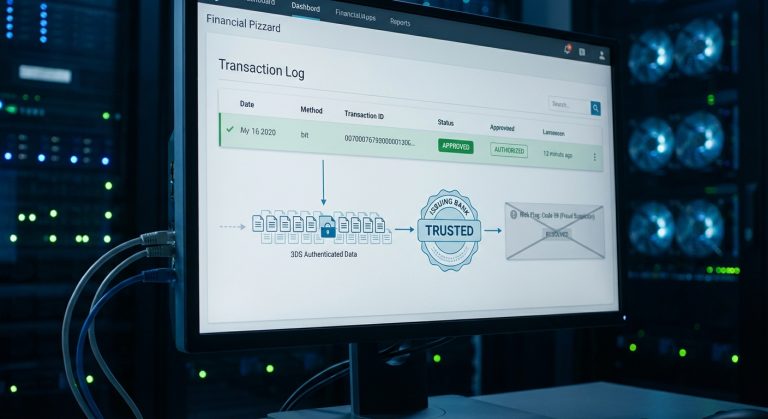
If a merchant’s risk engine or the payment gateway detects signals that might lead to a Code 59, stepping the user up to a 3D Secure challenge can preemptively solve the problem. By requiring the user to authenticate the purchase directly with their bank, often through a biometric prompt on their mobile banking app or a one-time password, the merchant effectively neutralizes the issuer’s primary concern.
When a transaction is fully authenticated, the liability for fraud typically shifts from the merchant to the issuing bank. Consequently, issuers are vastly more likely to approve a transaction that carries authenticated data, even if the geographic or velocity signals initially looked irregular. While introducing authentication does add a layer of friction to the checkout experience, an authenticated approval is always preferable to a silent hard decline.
Navigating the Customer Experience During a Decline
How a merchant communicates checkout issues to the customer plays a critical role in whether that customer tries again or abandons the brand forever. The messaging around Authorization Code 59 requires tact.
You should never present an error message telling a customer they are suspected of fraud, as that language is alarming and inherently accusatory. Instead, the user interface should frame the situation neutrally and constructively, placing the action in the context of security and protection.
A well-crafted error state might inform the customer that their bank has temporarily blocked the transaction to protect their account, followed by clear, actionable next steps. Advising the customer to check their mobile device for a security alert or suggesting they call the number on the back of their card empowers them to resolve the blocker. Once the flag is cleared with the issuer, the customer can safely return to complete the purchase, turning a potential lost sale into a successful payment recovery.
Complexities in Recurring Revenue Models
The dynamics of Code 59 change slightly when looking at subscription payment issues. In a recurring billing model, the initial transaction is often heavily scrutinized, but subsequent billing cycles generally enjoy higher approval rates because the pattern is established and predictable.
However, a perfectly healthy subscription can suddenly hit a wall of suspected fraud. This frequently occurs when the context of the card changes. For example, if the cardholder travels extensively and begins using their card in new locations, their bank might place a blanket freeze on the account, causing all subsequent automated subscription charges to fail with Code 59. Similarly, if the merchant changes their billing descriptor, processes the charge through a different regional acquiring entity, or alters the standard transaction amount, the issuer’s risk model might fail to recognize the established pattern and flag the renewal as suspicious.
To reduce payment declines in recurring models, merchants must ensure their automated billing systems are passing pristine, consistent data. Utilizing network tokens rather than raw primary account numbers can help maintain a stable, trusted connection with the issuer. Furthermore, automated retry logic for subscriptions flagged for fraud should be spaced out significantly, often by days rather than hours. This gives the cardholder ample time to notice the issue and resolve the hold on their account.
Transforming Decline Data into Strategic Insight
Mature organizations do not look at declined transactions in isolation. Instead, they view them as data points that map the health of their entire payment ecosystem. Tracking the frequency and distribution of Authorization Code 59 is a crucial part of this broader revenue optimization.
If a payment operations team notices a sudden spike in fraud declines, it requires immediate investigation. This spike could indicate an actual bot attack testing stolen cards against the merchant’s gateway, or it might point to a configuration error, such as a misaligned merchant category code or an issue with how the gateway formats billing addresses before passing them to the acquirer. In the United States, there were 323,459 cases of credit card fraud in the first half of 2025, a 51% increase from the year before (Source).
By continuously monitoring these decline cohorts, merchants can adjust their own internal risk thresholds. If genuine customers are consistently being flagged by issuers for high-value purchases, the merchant might choose to proactively route those specific transactions through an authentication flow, absorbing a small amount of user friction in exchange for a significantly higher final authorization rate.
The Long Game of Issuer Trust
Successfully navigating suspected fraud declines is ultimately about alignment. The issuing banks, the card networks, and the merchants all fundamentally want the same outcome. They want legitimate transactions flowing smoothly and fraudulent transactions stopped at the gate.
Authorization Code 59 is simply the ecosystem’s way of pausing the flow when the data does not add up. Merchants who treat this code as an annoying obstacle to be forcefully bypassed will continually struggle with poor authorization rates and strained acquiring relationships. Conversely, merchants who respect the signal, understand the mechanics behind the issuer’s decision, and build intelligent, patient, and communicative recovery workflows will naturally position themselves for optimal revenue capture.
Payment processing is not a static utility. It is a continuous dialogue between disparate systems. By passing clean data, utilizing authentication intelligently, and treating retries as a strategic operation rather than a brute-force mechanism, businesses can transform authorization challenges into sustainable, scalable growth.
Still letting failed transactions slip through?
SmartRetry turns declines into approvals - automatically, intelligently, and without changing your payment provider.
Frequently asked questions about this topic
Share this article
Author
Roi Lagziel
Roi Lagziel is a payments engineer specializing in authorization optimization, retry strategies, and issuer-level behavior. His work focuses on building practical, data-driven systems that help payment teams reduce false declines and recover lost revenue.
Read all articles >More in Payment Failures & Decline Codes:

March 8, 2026
The Hidden Mechanics of Cross-Border Card Declines
This article explains why international card transactions underperform, from issuer risk models to data mismatches and recurring billing gaps, and shows operators where to act to recover revenue and reduce false declines.

March 8, 2026
Issuer Response Code 43: Why Merchants Must Stop Retries on Stolen Cards
This article explains why Code 43 is a terminal decline, how to remove dead credentials from retry logic, and how disciplined handling protects approval rates, margin, and customer recovery.

March 8, 2026
Authorization Code 41: How Payment Teams Should Handle Lost Card Declines
This article explains why Code 41 is a definitive lost-card decline, how to stop harmful retries, and where account updater, tokenization, and targeted dunning improve recovery and authorization performance.