The Invisible Logic of 3D Secure: How Payment Teams Balance Fraud, Friction, and Revenue
March 8, 2026
12 min

The Invisible Logic of 3D Secure: Navigating Fraud, Friction, and Revenue Optimization
The world of online payments is a delicate balancing act. You want to let good customers in. You need to keep bad actors out. Every additional security check introduces friction into the user journey. Friction inevitably leads to checkout issues. Those checkout issues quickly translate into lost revenue. For years, merchants viewed 3D Secure as a necessary evil in this equation. It was the clunky, redirect-heavy hurdle that frustrated buyers. It tanked conversion rates in the name of regulatory compliance. Today, that narrative is fundamentally outdated. The modern 3D Secure framework operates largely in the shadows as a sophisticated, data-rich protocol. When implemented thoughtfully, it actually reduces payment failures rather than causing them, with card authorization rates in the UK at 90-96% for CNP transactions protected by 3D Secure versus 70-75% without it (Source). It transforms a rigid security checkpoint into a dynamic, continuous dialogue between the merchant, the payment service provider, and the issuing bank.
The Shift from Friction to Fluidity
To understand how experienced teams handle payment authorization today, it helps to acknowledge how much the underlying infrastructure has evolved. The original 3D Secure protocol was built for a desktop era. It relied heavily on static passwords and jarring pop-up windows that interrupted the user experience. It trained an entire generation of consumers to abandon their shopping carts the moment their bank asked them to remember a password they created five years ago.
The rollout of EMV 3D Secure (commonly known as 3DS2) changed the mechanics of this interaction entirely. Rather than relying on explicit user intervention for every transaction, the modern protocol was designed around the concept of frictionless authentication. It allows the merchant’s payment stack to package over a hundred discrete data points-ranging from device fingerprints and browser settings to shipping address history and typing cadence-and send them directly to the issuing bank in the background.
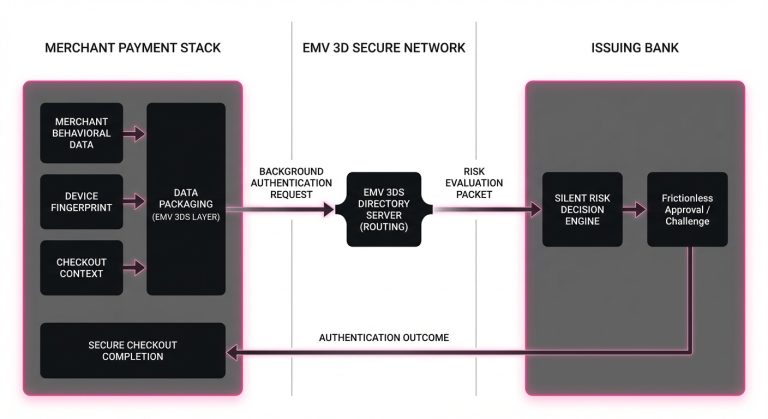
This rich data payload gives the issuer enough context to make a confident, instantaneous risk decision. If the data looks consistent with the cardholder’s historical behavior, the issuer approves the authentication silently. The customer simply clicks a button and sees a success screen, completely unaware that a complex security protocol just fired in the background. This frictionless flow is the gold standard of modern payment processing, bridging the gap between rigorous security and a seamless customer experience.
The Trade-off of the Step-Up
Of course, the frictionless flow is not guaranteed. When an issuer detects an anomaly-perhaps the transaction is unusually large, the device is new, or the user is purchasing from an unfamiliar location-they will trigger a “step-up” challenge.
In the modern era, this step-up rarely involves a static password. Instead, it relies on Out-of-Band (OOB) authentication or biometric verification. The user might receive a push notification on their phone asking them to open their banking app and authenticate via FaceID or a fingerprint. While this is objectively smoother than the old pop-up windows, it still introduces friction. A step-up challenge requires the user to take action, switch contexts, and successfully navigate back to the merchant checkout page. At any point in this chain, latency, confusion, or technical timeouts can occur, leading to an decline, and one report found 22% of payments authenticated using 3D Secure are lost (Source). Managing when and how this step-up happens is where strategic payment professionals focus their attention.
The Hidden Dialogue Inside the Payment Processing Flow
To influence the outcome of a transaction, you have to understand the underlying architecture of a 3D Secure request. The process is not a single, monolithic step. It is a rapid sequence of interactions between three distinct technical components: the 3DS Server (on the merchant or acquirer side), the Directory Server (operated by the card networks like Visa or Mastercard), and the Access Control Server (managed by the issuing bank).
When a customer initiates a payment, the merchant’s payment gateway sends the authentication payload to the 3DS Server. This server formats the data and forwards it to the appropriate card network’s Directory Server. The Directory Server acts as a high-speed router, identifying the specific issuing bank that owns the card and passing the request along to their Access Control Server (ACS).
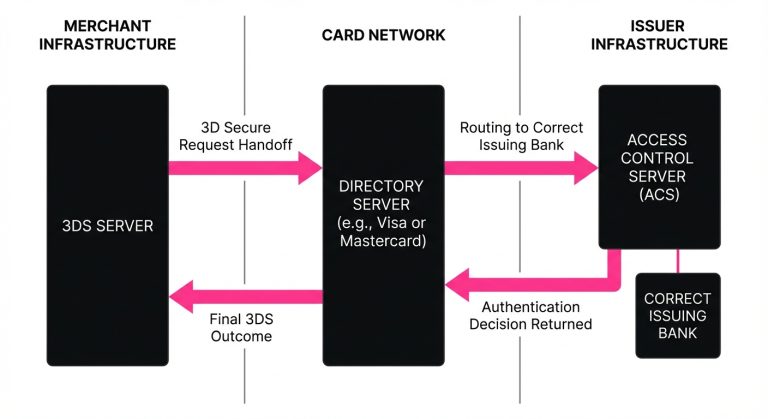
The ACS is the ultimate decision-maker in the 3DS flow. It evaluates the rich data payload against the bank’s proprietary risk models. In milliseconds, the ACS must decide whether to grant a frictionless approval or mandate a step-up challenge. The issuer response is then routed back through the chain to the merchant.
If the authentication is successful, the merchant proceeds with the actual payment authorization request, passing along a cryptographic token (the CAVV or AAV) that proves the user was authenticated. This token is the key to the entire system: it triggers the “liability shift.” When a transaction is successfully authenticated via 3DS, the financial liability for any subsequent fraud-related chargebacks shifts away from the merchant and onto the issuing bank.
3: The Art of Exemption Management
Because liability shift plays such a massive role in the economics of payments, navigating 3DS is rarely as simple as turning it on for every transaction. Sophisticated merchants do not blindly route all traffic through the 3DS rails. Instead, they utilize exemption strategies to optimize the flow.
In regions with strict regulatory frameworks, such as Europe under the Payment Services Directive 2 (PSD2), Strong Customer Authentication (SCA) is technically required for online card payments. However, the regulation includes specific exemptions that allow merchants and acquirers to bypass the step-up challenge under certain conditions. The most common of these is Transaction Risk Analysis (TRA).
Balancing Risk and Conversion
If a merchant’s acquirer maintains a very low overall fraud rate, they can request a TRA exemption for transactions up to a certain monetary value. By flagging the transaction with a TRA exemption, the acquirer is essentially telling the issuer, “Our risk models have vetted this transaction, and we believe it is safe. Let’s skip the 3DS challenge.”
The strategic catch here is liability. When an acquirer requests a TRA exemption, the liability for fraud remains with the merchant. The merchant is trading the protection of the liability shift for the conversion benefits of a frictionless checkout.
Furthermore, exemptions are requests, not guarantees. The issuer always retains the final say. If the issuing bank’s ACS looks at the transaction and decides the risk is too high-perhaps the cardholder has been targeted by fraud recently, or the bank is approaching its own regulatory fraud thresholds-the issuer will ignore the exemption request and issue what is known as a soft decline.
Why Do Perfectly Good Transactions Fail?
A soft decline is one of the most misunderstood mechanisms in modern payments. When a merchant attempts to process a payment authorization without 3DS (perhaps relying on an exemption or simply choosing not to authenticate), the issuer might reject the request with a specific response code.
To an unsophisticated payment setup, this looks like a standard transaction declined event. The merchant might display an error message to the user or give up entirely. But a soft decline is actually an invitation. The issuer is effectively saying, “I am willing to approve these funds, but I need you to step up the user with 3D Secure first.”
If the merchant’s payment stack is properly configured, it will catch the soft decline code, automatically pause the transaction, and instantly trigger a 3DS challenge to the user in real-time. Once the user authenticates, the payment is retried and approved. If the merchant misses this signal, they have needlessly caused a card declined scenario for a perfectly valid customer.
Technical Breaks and User Drop-offs
Beyond soft declines, 3D Secure can introduce failures purely through technical complexity. The Out-of-Band authentication flow requires the merchant’s checkout page to maintain an open session while the user interacts with their banking app.
If the user’s mobile network drops, if the banking app is slow to load, or if the ACS experiences a temporary outage, the 3DS session can time out. In these instances, the transaction fails not because the user was a fraudster, but because the connective tissue of the network temporarily frayed. Observing these patterns allows payment teams to adjust their timeout windows and user messaging to reduce payment declines caused by infrastructure hiccups rather than actual risk.
5: Solving the Recurring Revenue Puzzle
The complexities of 3D Secure become even more pronounced when dealing with recurring revenue models. For subscription-based businesses, introducing friction at checkout is only half the battle. The real challenge lies in ensuring that subsequent billing cycles process smoothly without requiring the customer to manually authenticate every month.
This brings us to the operational reality of Merchant Initiated Transactions (MITs). When a customer signs up for a subscription, their initial checkout is considered a Customer Initiated Transaction (CIT). It is crucial that the merchant processes this initial CIT with a full 3D Secure authentication. Doing so proves to the issuing bank that the cardholder is present, willing, and authorizing the future billing agreement.
The Power of the Network Token
Once the CIT is successfully authenticated, the merchant can flag all subsequent recurring payments as MITs. Because the initial mandate was secured, issuing banks tend to view subsequent MITs with a high degree of trust, allowing them to process without 3DS challenges.
However, subscription payment issues still arise. Cards expire, issuing banks update their risk models, or technical flags are misaligned in the recurring payment payload. If an MIT is declined, it puts the merchant in a difficult position. Because the customer is not actively in a checkout session, the merchant cannot dynamically trigger a 3DS challenge. They must rely on specialized recovery workflows, often involving email or SMS outreach, to bring the customer back on-session to re-authenticate the card.
What Happens Next: Rethinking the Recovery Flow
When a payment fails-whether due to an ACS timeout, a hard decline for insufficient funds, or a mismanaged soft decline-the immediate reaction of many legacy systems is to aggressively resubmit the transaction. This brute-force approach to retrying payments is not only ineffective, but it can actively harm a merchant’s standing with card networks and issuers.
Modern intelligent recovery relies on intelligent orchestration rather than sheer volume. It requires parsing the exact issuer response, understanding the specific decline code, and making a probabilistic decision about the next best action. If a transaction failed because the issuer’s ACS was temporarily unresponsive, a delayed retry might succeed. If it failed due to an improperly formatted MIT flag, the payload needs to be adjusted before it is resubmitted.
Platforms like Smart Retry exist precisely to untangle this complexity, focusing on payment optimization and intelligent retries of declined payment transactions, helping merchants recover revenue and improve transaction authorization rates. By analyzing historical issuer behavior and understanding the nuanced signals embedded in decline codes, these systems can adapt the recovery flow dynamically, ensuring that retries are executed only when they have a statistical likelihood of success, thereby protecting the merchant’s authorization ratios.

The Nuance of Retry failed payments
The strategy behind how to retry failed payments involves significant operational restraint. Issuers actively monitor merchant retry velocity. If a merchant ID (MID) is seen endlessly hammering the network with identical, failing requests, the issuer’s risk engine will likely start shadow-banning that merchant, resulting in higher overall decline rates across perfectly healthy transactions.
Intelligent recovery flows look at the broader context. Is it the end of the month when card balances might be depleted? Was the decline related to a localized banking outage? Did the 3DS authentication fail due to a user timeout or a network timeout? By answering these questions programmatically, payment teams can orchestrate a recovery sequence that maximizes revenue while maintaining a pristine reputation with the issuing banks.
Peering Into the Issuer Risk Model
To truly optimize a payment stack, one must attempt to view the ecosystem from the perspective of the issuing bank. Issuers are not monoliths, and they do not process 3DS requests identically.
A large, technologically advanced digital bank might rely heavily on the rich data elements of EMV 3DS to grant frictionless approvals almost universally, stepping up only the most anomalous behavior. Conversely, a smaller regional credit union might rely on older, more rigid risk parameters, issuing step-up challenges at a much higher frequency regardless of the data payload provided.
These differences manifest at the BIN level. Experienced payment teams often analyze their approval rates by BIN to understand specific issuer tendencies. If they notice that a particular issuer consistently rejects TRA exemptions and forces step-ups, they might stop requesting exemptions for that specific BIN entirely, opting instead to pass the full 3DS data payload upfront to ensure the smoothest possible authentication flow.
Issuers also track the historical fraud rates associated with specific merchants. If a merchant consistently passes high-quality data and maintains low fraud, issuers learn to trust that merchant’s traffic. This trust translates directly into higher frictionless approval rates. Conversely, if a merchant attempts to game the system by aggressively bypassing 3DS on risky traffic, issuers will quickly adjust their models, subjecting that merchant’s customers to increased friction. In regulated markets like Europe and Australia, fraud rates for CNP transactions protected by 3DS were reported as 3 to 6 times lower than for all CNP transactions (Source).
The Next Frontier in Payment Performance
The evolution of 3D Secure reflects a broader maturation in the payments industry. We have moved past the era where security and user experience were viewed as a zero-sum game. Today, the most successful payment operations recognize that authentication, when handled intelligently, is a powerful commercial lever.
Navigating this landscape requires moving away from static rules and embracing dynamic, data-driven strategies. It means understanding the intricate dialogue between the merchant plug-in, the directory server, and the access control server. It involves managing exemptions strategically, parsing soft declines accurately, and rethinking how recovery flows are designed.
By treating 3D Secure not as a regulatory burden, but as an opportunity to build trust with issuing banks and streamline the customer journey, merchants can fundamentally alter their unit economics. The complexity of the network remains invisible to the end user, but for the teams orchestrating the flow behind the scenes, mastering these mechanics is the ultimate key to sustained revenue growth.
Still letting failed transactions slip through?
SmartRetry turns declines into approvals - automatically, intelligently, and without changing your payment provider.
Frequently asked questions about this topic
Share this article
Author
Roi Lagziel
Roi Lagziel is a payments engineer specializing in authorization optimization, retry strategies, and issuer-level behavior. His work focuses on building practical, data-driven systems that help payment teams reduce false declines and recover lost revenue.
Read all articles >More in Payment Approval Optimization:

April 16, 2026
Why Transaction Approval Rate Is Misleading and What Payment Teams Should Measure Instead
This article explains why blended approval rate can distort payment decisions and how teams can use recovery, cohort, and retry metrics to protect revenue and reduce false declines.

March 8, 2026
Why Virtual Card Payments Fail in Travel and How Payment Teams Improve Approval Rates
This article explains why travel virtual cards fail at hotels and what operators can do to recover approvals, cut manual intervention, and protect margins across issuing and acquiring.

March 8, 2026
Beyond the Monolith: Why Global Scale Demands a Multi-Acquirer Mindset
This article explains how multi-acquirer setups, local routing, and smarter retries help payments operators lift approvals, cut false declines, and protect revenue as global volume grows.