The Silent Revenue Killer: Decoding the Mechanics of False Declines
March 8, 2026
12 min

The Silent Revenue Killer: Decoding the Mechanics of False Declines
You have built an incredible product. Your marketing team successfully guided a new customer through the funnel. The buyer is ready. They enter their payment details. They click the purchase button. Then, the screen loads, and a frustrating message appears: payment declined. In an instant, the momentum of the sale breaks. Most organizations treat these payment failures as an unavoidable cost of doing business. They look at their reporting dashboards, see a rejected transaction, and naturally assume the buyer simply lacked funds or the system caught a fraudster in the act. But the reality of modern digital commerce is far more complex. A significant percentage of these rejections are actually false declines, meaning they are entirely legitimate transactions blocked by hyper-cautious banking systems. Understanding the intricate mechanics behind these silent revenue killers fundamentally changes how you approach financial operations. By decoding the underlying signals, you can recover lost revenue, preserve your customer experience, and stop leaving perfectly good money on the table.
The Invisible Leak in the Growth Bucket
In the modern digital economy, growth is fiercely fought for. Teams spend vast amounts of time, energy, and capital optimizing landing pages, tweaking ad copy, and reducing friction in the user experience. Yet, when the customer finally reaches the bottom of the funnel, control is largely handed over to a labyrinth of external financial networks.
When a transaction fails, the immediate assumption is often that the system worked exactly as intended. The fraud filters did their job, or the customer’s account simply lacked the necessary funds. While true in many cases, industry data repeatedly shows that a surprisingly high volume of declined transactions come from customers with adequate funds and zero malicious intent. Merchants reject 6% of all eCommerce orders and between 2% and 10% of rejected eCommerce orders are legitimate.
These false declines represent a unique kind of operational pain. You have already paid the customer acquisition cost. The buyer has already demonstrated high intent. When the system rejects them, you lose not only the immediate cart value but also the potential lifetime value of that customer. Faced with friction at checkout, a motivated buyer rarely reaches out to customer support to troubleshoot; they simply open a new tab and purchase from a competitor. This invisible leak drains top-line revenue quietly, often masked behind aggregate data that simply groups all rejections under a single, unhelpful banner.

The Anatomy of the 200-Millisecond Journey
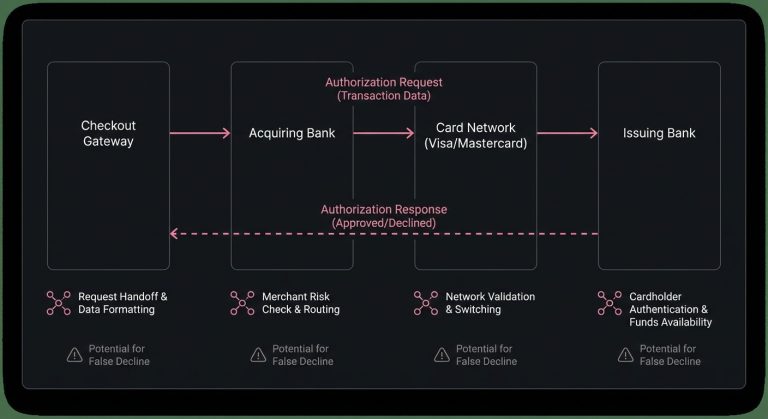
To understand why good transactions fail, we have to look at the payment processing flow. When a customer clicks the buy button, they initiate a highly complex relay race that typically concludes in under a fraction of a second.
The transaction data travels from your checkout gateway to your acquiring bank. The acquirer formats this request and sends it to the relevant card network, such as Visa or Mastercard. The network then routes the request to the issuing bank-the institution that actually provided the credit or debit card to the customer. The issuer’s authorization system evaluates the request, makes a split-second decision, and sends a response back down the chain.
On the surface, this relay is a marvel of modern engineering. In practice, it is a highly lossy process.
The Challenge of Data Degradation
When a customer is on your website, you have a rich, multi-dimensional view of their behavior. You know their IP address, their device fingerprint, how long they lingered on a specific product page, and their historical purchasing patterns with your brand.
However, as the transaction request moves from your gateway through the acquiring network and finally to the issuer, much of this rich contextual data is stripped away. The request is translated into a standardized format designed decades ago to prioritize speed and network efficiency. By the time the transaction reaches the issuing bank, the rich narrative of an excited buyer has been reduced to a handful of basic data points: an account number, a transaction amount, a card network, and perhaps a zip code. The issuer is forced to make a definitive financial decision based on an incredibly narrow view of the event.
The Issuer’s Dilemma: Managing Risk in the Dark
Issuing banks operate under a heavy burden of liability. When a fraudulent transaction slips through, the issuer often absorbs the cost, the administrative burden of handling the chargeback, and the reputational damage with their cardholder. Consequently, their risk models are inherently conservative. They operate on a defensive footing, essentially treating unusual transactions as guilty until proven innocent.
When evaluating a payment authorization request, the issuer’s machine learning models look for anomalies. If the transaction deviates from the cardholder’s usual behavior, or if the merchant falls into a statistically higher-risk category, the model’s confidence score drops. If that score dips below a predefined threshold, the system automatically denies the request to protect the account.
The issuer does not know that the customer is buying a legitimate gift for a family member in another state, or that they are using a corporate VPN that masks their true location. The issuer only sees a data pattern that faintly resembles historical fraud, and they pull the plug.
Deciphering the Ambiguity of Decline Codes
When an issuer decides to block a transaction, they send back a standardized response code. In a perfect world, these codes would provide clear, actionable feedback to the merchant. In reality, the issuer response is often intentionally vague.
The most notorious of these is the generic “Do Not Honor” code. Historically, this code indicated that the merchant should physically confiscate the card and call the bank. Today, it serves as a catch-all category. Issuers frequently use ambiguous codes to avoid tipping off sophisticated fraudsters about the exact parameters of their risk models. While this protects the bank’s proprietary security logic, it leaves honest merchants guessing. A “Do Not Honor” code could mean the account is flagged for fraud, the card is expired, the velocity of purchases is too high, or the bank’s internal systems are simply undergoing maintenance.
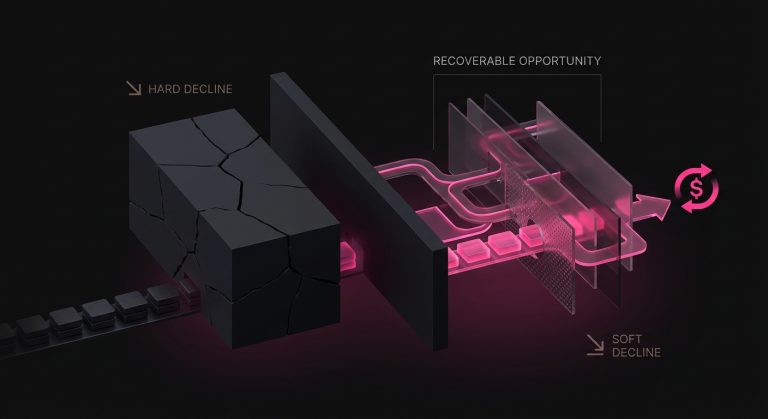
Categorizing the Rejection: Soft vs. Hard Declines
To mount an effective defense against revenue loss, we must differentiate between the two primary categories of transaction failures: hard declines and soft declines.
A hard decline represents a permanent barrier. The issuer is communicating that this transaction will never succeed under its current parameters. This happens when a card is reported stolen, an account is officially closed, or the card number itself is entirely invalid. Attempting to process a hard decline again is an exercise in futility.
A soft decline, however, represents a temporary state of friction. The issuer is effectively saying “not right now” or “not under these exact conditions.” The underlying account is valid, but a specific environmental factor triggered a block. Perhaps the network timed out, the daily spending limit was temporarily breached, or the issuer’s fraud model was overly sensitive at that specific moment. Soft declines are where revenue recovery is not just possible, but highly probable if handled correctly.
Common Triggers That Sabotage Good Transactions
Understanding the specific environmental factors that lead to decline allows teams to anticipate and mitigate them. While issuer algorithms are closely guarded secrets, several common patterns consistently trigger defensive rejections.
- Unexpected Velocity and Volume: If a cardholder typically uses their card for small, infrequent purchases and suddenly attempts a high-value transaction, the risk model will likely flag it. Similarly, if multiple transactions hit the card in rapid succession-even small ones-the system may interpret this as a fraudster testing a stolen card via a script.
- Geographic and Cross-Border Friction: Transactions processed across borders naturally carry higher decline rates. If an acquiring bank is based in Europe, but the customer’s issuing bank is a regional credit union in the American Midwest, the issuer may reject the unfamiliar international request out of an abundance of caution, even if the customer is sitting on their couch at home.
- Data Formatting Nuances: The global financial system relies on highly specific data formatting. If your gateway passes an Address Verification System request where the postal code format slightly mismatches the issuer’s legacy database, the transaction might be rejected. Even minor discrepancies in how a merchant name or merchant is presented can trip older risk filters.
- Recurring Billing Fatigue: Subscription-based businesses face unique challenges. When a card is stored on file for monthly billing, the issuer’s risk tolerance can change over time. What was approved in January might be declined in July due to shifting internal policies, expired credentials, or general subscription payment issues, even if the underlying account remains perfectly healthy.
The Hit Refresh Fallacy: Why Immediate Resubmission Fails
When faced with a soft decline, the natural human instinct is to simply try again. If a website fails to load, we refresh the browser. Many merchants apply this exact logic to their billing systems, automatically resubmitting a declined transaction mere seconds or minutes after the initial failure.
This approach is highly counterproductive. If an issuer’s algorithm just rejected a transaction because it suspected anomalous behavior, immediately hitting the system with the exact same request from the exact same merchant does not build confidence. In fact, it reinforces the algorithm’s suspicion that it is under attack by an automated script.
Blind, rapid retries not only guarantee a subsequent failure, but they also actively harm your relationship with the payment network.
The Risk of Algorithmic Penalties
Card networks and issuers monitor merchant behavior closely. If a merchant habitually submits the same failed transactions over and over, their overall approval rate plummets. Issuers notice when a specific merchant sends a high volume of un-optimized, repetitive traffic. Over time, the issuer’s algorithms may begin to view the merchant itself as a risk vector.
Once a merchant’s trust score with an issuer degrades, the issuer will apply stricter scrutiny to all transactions originating from that source. A poor retry strategy can inadvertently drag down your baseline approval rates for entirely new, healthy customers. Therefore, the goal is not simply to retry, but to retry intelligently.
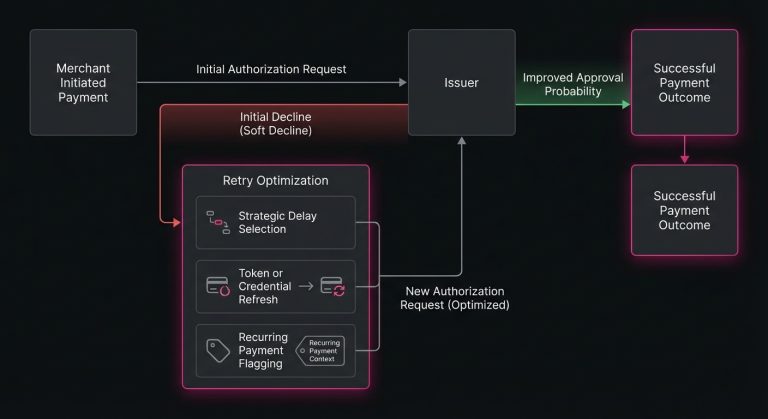
Engineering the Recovery: The Science of Strategic Delays
The secret to successfully recovering soft declines lies in altering the context of the request. If the exact same request failed at 10:00 AM, sending it again at 10:01 AM yields no new information to the issuer. However, introducing strategic delays changes the environmental variables.
Many soft declines resolve themselves organically if given enough time. A temporary hold on an account may expire after a few hours. A customer who hit their daily spending limit on a Tuesday will have that limit reset by Wednesday morning. If an issuer’s internal authorization server was experiencing a minor outage or load-balancing issue, waiting a few hours allows the network to stabilize.
The timing of a retry is a critical optimization lever. Experienced operators analyze historical data to identify the optimal windows for resubmission. They map out the cardholder’s local timezone to ensure retries occur during standard daylight hours, avoiding suspicious middle-of-the-night processing. They look at calendar patterns, understanding that retry attempts clustered around the 1st or the 15th of the month align with typical payroll cycles, significantly increasing the probability that an account has been replenished.
Applying Context to the Request
Beyond timing, altering the actual data payload can shift the issuer’s perspective. For recurring transactions, leveraging network tokenization can drastically improve outcomes. When merchants use a secure network token instead of a raw Primary Account Number, the card network actively updates the token lifecycle in the background. If the customer receives a new physical card with a new expiration date, the token remains valid, allowing the transaction to process smoothly without requiring the customer to manually update their profile.
Similarly, adjusting the specific flags sent to the issuer can clarify the intent. Properly flagging a transaction as a merchant-initiated recurring payment, rather than a fresh customer-initiated checkout, signals to the issuer that there is an existing, trusted relationship between the buyer and the seller. Providing this context lowers the perceived risk and encourages the algorithm to grant an approval.
Automating Revenue Rescue
Building an internal system to handle this level of transactional nuance requires significant engineering resources. Analyzing decline codes, mapping out temporal retry schedules, managing token lifecycles, and constantly adapting to the shifting risk models of thousands of different issuing banks is a monumental task. For most organizations, attempting to build and maintain this logic in-house distracts from their core product development.
This is precisely where specialized infrastructure becomes valuable. Platforms like SmartRetry focus entirely on the science of payment optimization, actively analyzing the intricate variables behind declined transactions to orchestrate intelligent, data-driven resubmissions. By programmatically determining the exact right moment and the optimal routing configuration to retry failed payments, these systems help merchants effortlessly recapture lost revenue and elevate their overall transaction approval rate, all without manual intervention.
Building a Resilient Payment Ecosystem
Viewing payment declines as a binary outcome of either success or failure is an outdated perspective. The modern financial ecosystem is highly probabilistic. Every transaction is a negotiation between interconnected systems, each trying to balance the desire for commerce with the necessity of security.
When you shift your perspective from reactive frustration to proactive optimization, false declines cease to be an unavoidable cost of doing business. They become an addressable engineering challenge. By respecting the constraints of the issuer, avoiding the temptation of blind repetition, and systematically applying context and strategic timing to your recovery efforts, you build a remarkably resilient revenue engine. You ensure that the friction of the global financial network does not penalize the customers who actively want to do business with you. Ultimately, protecting your payment flow is one of the most direct, impactful ways to honor the hard work your team put into acquiring that customer in the first place.
Still letting failed transactions slip through?
SmartRetry turns declines into approvals - automatically, intelligently, and without changing your payment provider.
Frequently asked questions about this topic
Share this article
Author
Roi Lagziel
Roi Lagziel is a payments engineer specializing in authorization optimization, retry strategies, and issuer-level behavior. His work focuses on building practical, data-driven systems that help payment teams reduce false declines and recover lost revenue.
Read all articles >More in Payment Failures & Decline Codes:

March 8, 2026
The Hidden Mechanics of Cross-Border Card Declines
This article explains why international card transactions underperform, from issuer risk models to data mismatches and recurring billing gaps, and shows operators where to act to recover revenue and reduce false declines.

March 8, 2026
Issuer Response Code 43: Why Merchants Must Stop Retries on Stolen Cards
This article explains why Code 43 is a terminal decline, how to remove dead credentials from retry logic, and how disciplined handling protects approval rates, margin, and customer recovery.

March 8, 2026
Authorization Code 41: How Payment Teams Should Handle Lost Card Declines
This article explains why Code 41 is a definitive lost-card decline, how to stop harmful retries, and where account updater, tokenization, and targeted dunning improve recovery and authorization performance.