Google Pay Declines: How Wallet Payloads, Tokens, and Retries Impact Authorization
March 8, 2026
11 min

Load video
The checkout experience has continuously evolved to meet customer expectations for frictionless interactions. Digital wallets deliver exactly that, with a quick biometric scan often completing a purchase in seconds. Yet, beneath this simple consumer interface lies immense architectural complexity. Google Pay is not a monolith. Instead, it acts as an intricate orchestration layer passing tokenized credentials, device data, and cryptograms between the consumer, the merchant, and the acquiring bank. For teams focused on revenue optimization, understanding this underlying plumbing is critical. When a seemingly perfect wallet interaction results in a declined transaction, the recovery effort requires more than a simple blind resubmission. It demands a granular understanding of how issuing banks process, evaluate, and occasionally misinterpret digital wallet payloads.
Beyond the Button: Deconstructing the Payload
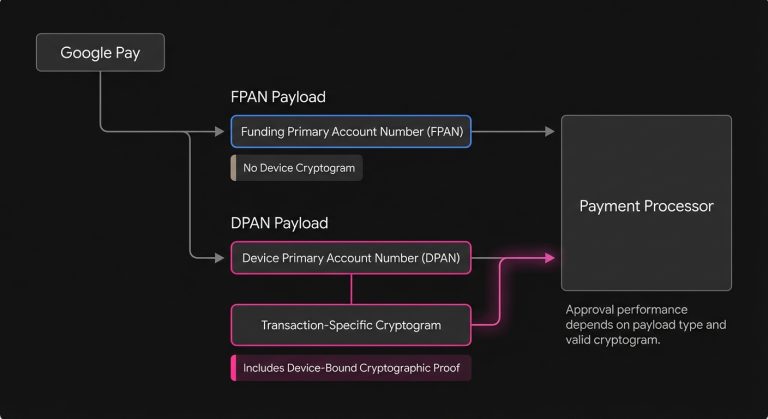
To optimize a checkout flow, it helps to look past the branding and examine exactly what Google Pay hands to your payment processor. Unlike a traditional credit card entry, a digital wallet payload is a dynamic package of data. Depending on how the user interacts with the wallet, the underlying credential takes one of two primary forms. It will either be a traditional Funding Primary Account Number (FPAN) or a Device Primary Account Number (DPAN).
Understanding the distinction between these two formats is the first step in diagnosing payment processing flow anomalies. An FPAN transaction via Google Pay typically occurs when a user saves their card details in their Google account, such as Chrome autofill, but has not provisioned the card to a physical device. To the issuing bank, this often looks suspiciously like a standard card-on-file ecommerce transaction that lacks the cryptographic proof of device possession.
Conversely, a DPAN is a network token specific to the user’s device. When a customer uses a card provisioned to their Android phone or Wear OS watch, Google Pay generates a unique cryptogram for that specific transaction. This cryptogram serves as mathematical proof that the payment originated from the authenticated device. DPANs are the gold standard for merchants because they carry higher inherent trust, bypass certain regulatory friction points, and generally yield a much higher transaction approval rate than their FPAN counterparts.
The Role of the Cryptogram
When a DPAN is utilized, the transaction payload includes a cryptogram generated by the token service provider, typically Visa or Mastercard. This dynamic, single-use code validates the domain, transaction amount, and device. Issuing banks rely heavily on this data to make split-second risk decisions. If a processor fails to format or pass the cryptogram correctly, the transaction loses its trusted status and authorization performance suffers.
Implicit Authentication and SCA
In regions governed by Strong Customer Authentication (SCA) mandates, such as Europe’s PSD2, the DPAN payload offers a distinct structural advantage. Because the user unlocks their device via biometrics or a PIN before tapping or clicking, the authentication is handled implicitly by the operating system. Proper formatting signals to the issuer that two-factor authentication has already occurred. This delegated authentication model reduces the need for cumbersome Strong Customer Authentication, keeping the checkout flow fast and abandonment rates low. See also The Invisible Logic of 3D Secure: How Payment Teams Balance Fraud, Friction, and Revenue.
The Illusion of Invincibility: Why Trusted Payloads Fail
It is tempting to view biometric, tokenized wallet payments as immune to failure. The user is verified, the token is secure, and the data is pristine, yet payment issues persistently occur. Even the most perfectly formatted Google Pay payload remains subject to the harsh realities of consumer finance and legacy banking infrastructure.
A common misconception is that a tokenized payment acts as a guarantee of funds, but it does not. While network tokens heavily suppress fraud-related declines, they do nothing to solve for insufficient funds, closed accounts, or restrictive spending limits. When a declined message surfaces on a Google Pay transaction, the root cause is often completely decoupled from the technology of the wallet itself.
Deciphering the Issuer Perspective
Issuing banks operate on distinct, highly guarded risk models. Some legacy issuers maintain rigid velocity rules that treat rapid succession transactions suspiciously regardless of the cryptogram’s validity. If a user makes three rapid purchases via Google Pay, the legacy fraud engine might trigger a decline simply based on transaction velocity. Furthermore, if the underlying funding card has expired, certain issuers may still reject the transaction due to internal database mismatches, even if the network token theoretically updates automatically.
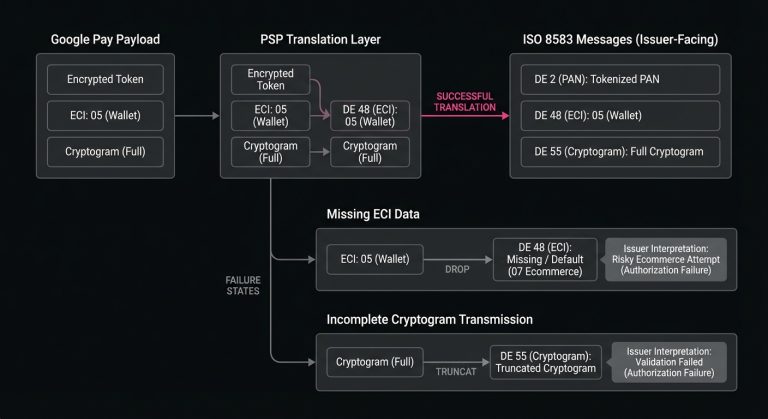
The Processor Translation Layer
Another frequent point of failure lies between the merchant and the acquirer. Payment service providers (PSPs) must translate the raw Google Pay payload into standard ISO 8583 messages for the card networks. If a PSP inadvertently strips the Electronic Commerce Indicator (ECI) flag or truncates the cryptogram during this translation, the issuer receives an incomplete message. From the bank’s perspective, a high-trust DPAN suddenly looks like a high-risk and unauthenticated ecommerce attempt, leading to an immediate soft decline.
The Subscription Paradox: Wallets in Recurring Flows
One of the most complex areas of digital wallet optimization involves recurring revenue models. Google Pay is designed primarily to facilitate friction-free single-click purchases. Adapting this technology to handle ongoing billing cycles introduces a unique set of architectural challenges. If these integrations are not carefully managed, they often result in complex subscription payment issues.
The initial purchase, known as a Customer Initiated Transaction (CIT), is generally straightforward. The user is present to authenticate the device and generate the cryptogram. However, when the merchant needs to bill that same user next month for a subscription, the customer is no longer present. This subsequent charge is processed as a Merchant Initiated Transaction (MIT).
To execute an MIT successfully using Google Pay credentials, the merchant must rely on the network token generated during the initial checkout. The challenge arises because not all processors map the initial CIT to the subsequent MIT seamlessly. If the MIT payload lacks the proper reference to the original authenticated transaction, the issuer’s risk engine will flag it as an unauthorized attempt on a tokenized credential. Establishing a robust token lifecycle management system is essential to maintaining revenue continuity in subscription businesses. This requires ensuring that the network token is securely stored and correctly referenced in all future billing cycles.
Intelligent Recovery: Navigating Post-Decline Logic
When a tokenized wallet transaction is rejected, the immediate reaction of the payment system dictates whether that revenue is lost or recovered. Traditional retry logic blindly resubmits the exact same payload at predetermined intervals, which is increasingly ineffective and often counterproductive. Repeatedly hammering an issuing bank with a failed DPAN can trigger velocity lockouts, transforming a temporary soft decline into a permanent hard decline. See our guide Decoding Hard and Soft Declines: A Practical Guide to Smarter Payment Recovery for more on this topic.
To effectively retry failed payments, systems must parse the specific issuer response code and adjust the recovery strategy accordingly. A decline for insufficient funds requires a temporal delay. This allows the consumer time to replenish their account, perhaps by aligning the retry with common payroll cycles. Conversely, a soft decline related to a suspected fraud flag on a tokenized transaction might require stepping the user up to a traditional 3D Secure flow or prompting them to utilize a different funding source entirely. For more on fraud declines and recovery, see Decoding Authorization Code 59: How Suspected Fraud Declines Affect Payment Recovery.
Platforms like SmartRetry address this specific operational layer by focusing on intelligent retries of declined payment transactions. They analyze issuer behaviors, temporal patterns, and response codes. By dynamically adjusting the timing and structure of the retry attempt based on the exact reason for failure, merchants can recover revenue more efficiently. This improves transaction authorization rates without introducing unnecessary friction into the customer experience.
Parsing the Decline Codes
Understanding the nuance between different decline codes is critical for a smart recovery strategy. A Do Not Honor code, often mapped to an 05 response, is notoriously ambiguous. While it might indicate fraud on a standard card, this same code on a Google Pay DPAN frequently points to a token mapping error at the issuer level or a mismatch in the MIT framework. Treating these distinct scenarios with the same blunt retry logic ensures suboptimal recovery rates. See also How to Recover 05 Do Not Honor Declines With Smarter Payment Retries.
The Role of Network Lifecycle Updates
Another critical element of recovery involves keeping the token data fresh. Visa and Mastercard both offer Account Updater services that automatically refresh compromised or expired credentials. For merchants utilizing Google Pay network tokens, ensuring the processor actively queries these lifecycle updates before initiating a retry can salvage transactions that would otherwise fail due to stale underlying card data.
Acquirer Routing and Fallback Strategies
For enterprise merchants operating across multiple geographies, a single-acquirer setup often limits the optimization potential of digital wallets. Different acquiring banks maintain varying relationships and routing efficiencies with regional issuers. An authorization attempt that fails through one acquirer might succeed through another simply due to how the data is packaged and transmitted to the specific issuing bank. Identifying the issuing bank is often a first step; use our Card Issuer Lookup tool to find the issuing bank and card network for any payment card.
Implementing intelligent routing for Google Pay transactions requires a deep understanding of processor performance. Some acquirers excel at processing DPANs in North America but struggle with the specific SCA compliance flags required in European markets. By monitoring authorization rates at the processor and Bank Identification Number (BIN) level, merchants can dynamically route wallet payloads to the acquirer with the highest historical probability of success. The BIN Lookup Tool helps identify card type and country of origin, facilitating this process.
If an issuer consistently struggles to process DPANs correctly, falling back to a traditional card-entry flow might be the most pragmatic way to secure the transaction, even though it introduces more friction. The goal is not to force a specific technology. Instead, merchants should engineer a resilient checkout ecosystem that adapts to the real-time processing capabilities of the broader financial network.
Testing and Simulation in Wallet Environments
Optimization is impossible without rigorous and continuous testing. Simulating digital wallet behaviors in a staging environment, however, presents unique obstacles. Unlike traditional test cards where a merchant can simply input a dummy number to simulate a decline, Google Pay relies on live device parameters, actual bank tokens, and real-time cryptographic generation.
To properly map out the payment processing flow and observe how different systems handle DPANs, engineering teams must maintain physical test devices provisioned with active network tokens. They must intentionally trigger various decline scenarios, such as velocity limits, expired cards, and cross-border mismatches, to observe how their PSP translates the issuer response. This empirical data informs the routing rules and recovery logic. Ultimately, it ensures that when a live customer experiences friction, the system reacts predictably and optimally.

Monitoring Authorization Deltas
A mature payment operations team does not just look at a blended approval rate. Instead, they isolate Google Pay performance from standard card-on-file performance and further divide those metrics between FPAN and DPAN traffic. By establishing these strict baselines, teams can spot anomalies rapidly. If the DPAN approval rate drops by two percentage points following a processor API update, the team knows exactly where to look rather than hunting blindly through the entire checkout architecture.
The Operational Mindset for Wallet Optimization
Treating a digital wallet merely as an alternative payment button is a missed opportunity. It operates as a distinct and complex authorization channel that interacts with the card networks and issuing banks under an entirely different set of rules. The presence of biometric authentication and network tokenization offers merchants a powerful lever to improve baseline authorization performance, provided the data is handled with precision throughout the entire transaction lifecycle.
The true work of optimization begins the moment a transaction is initiated and continues long after a decline occurs. It involves ensuring pristine payload translation at the PSP level, architecting a flawless MIT structure for recurring billing, and deploying intelligent recovery strategies when inevitable failures arise. Because consumer behavior heavily favors the convenience of device-based payments, with Google Pay reaching around 820 million active users globally in 2025 (Source), merchants who invest the time to understand and manage this underlying complexity will find themselves operating with a distinct and measurable advantage in revenue capture.
Still letting failed transactions slip through?
SmartRetry turns declines into approvals - automatically, intelligently, and without changing your payment provider.
Frequently asked questions about this topic
Share this article
Author
Roi Lagziel
Roi Lagziel is a payments engineer specializing in authorization optimization, retry strategies, and issuer-level behavior. His work focuses on building practical, data-driven systems that help payment teams reduce false declines and recover lost revenue.
Read all articles >More in Smart Payment Retry Strategies:

March 8, 2026
Decoding Hard and Soft Declines: A Practical Guide to Smarter Payment Recovery
This guide explains how to classify payment declines, respond with the right retry strategy, and reduce unnecessary churn, fees, and approval-rate drag across checkout and recurring billing.

March 8, 2026
The Boomerang Effect: Why Brute-Force Retries Cost More Than They Recover
This article explains why blind payment retries erode issuer trust, add network costs, and hurt future approvals, and how smarter decline management can improve recovery and authorization performance.

March 8, 2026
The Art of the Second Chance: Decoding Soft vs. Hard Declines
This article explains how to separate recoverable declines from permanent failures, optimize retry logic, and reduce involuntary churn to protect revenue and improve approval performance.